Read Part 1 of The 12 Days of Cyber-Mas Secure here.
Day 5: Review your privacy settings
Use the privacy settings of apps such as Facebook and Twitter to review who can see your posts. Facebook, for example, now has a security feature where you can change public posts into posts seen only by a select audience. The images below show how you can select “Limit Past Posts” to change old posts to just Friends.


Be aware that many other apps have default settings that may be less private than you would want so spend time checking them all.
Day 6: Review extent to which you disclose location
Rule of thumb: If there is no need to disclose your location, opt not to.
Some people love to geotag themselves – where they dined, where they traveled, where they are at the moment. If you are one of those who do this, be aware that your pattern of movements can give you away. Someone who is able to gain access to your locations from different apps can piece together a lot of things about yourself.
Location-based apps like Waze and Google Maps require access to your location but you can always tweak your settings so that you only allow access while using the app. Swarm, for example, is an app that lets you check into places with friends. This is the time to review who you accepted as friends in Swarm (and do some purging, if necessary) because those persons will know a lot about your dining, travel, and personal preferences. If you really want to check in, do so only AFTER you have left the place.
Long holidays like the Christmas break are also the times when bad elements are on the lookout for homes to target. Do not post your travel plans or vacation photos online while you are away.
Day 7: Run antivirus and security software
Does your laptop or mobile device have a good antivirus and/or privacy software? It’s time to get yourself one like Avast, AVG, Norton, McAfee or one of the other popular antivirus software in the market.
Set scheduled antivirus scans so it automatically scans regularly.
Day 8: Backup, backup, backup
This cannot be emphasized enough. If the contents of your mobile devices and laptops are crucial to your business or daily life, you cannot afford NOT to have backups.
This season, backup your contacts, important files, and applications. Mac users can do this using Time Machine. Cloud backups are also great but do so only with platforms that are known to have tight security measures. iCloud, Dropbox, Google Drive are some of the well-known platforms for keeping backups. If you have a portable external drive, you can also manually copy important files to it.
Day 9: Use disposable email addresses
This tip is not too popularly followed but it is one that is highly recommended if you want to reduce the amount of spam email you get — Use a disposable email address.
The moment you fill out online forms, subscribe to a newsletter, avail of that free ebook, or sign up for any online service, an email address has to be provided. If you regularly provide your primary email address for these activities, you may find your email overwhelmed by spam. There are many sites that offer disposable or throwaway email addresses. Personally, one of the sites I use is Tutanota. Creating disposable email addresses is very easy with Tutanota and your email mailbox is encrypted too.
Day 10: Activate automated alerts
An effective security measure that allows you to immediately react to a possible hack or intrusion into your accounts is to automate alerts – by SMS, email and/or mobile notification. Notifications can be bothersome at times, especially if you get too many. But there are some that you will be thankful for. Activate alerts for the following types of activities, among others:
- Invalid login attempts
- Password changes or requests to change password
- Purchases using credit cards
- ATM withdrawals
Day 11: Revoke access by rarely used apps
You may have linked some apps years ago that you no longer actively use or which may have slowly faded away into oblivion. Check all your app settings and revoke access by these apps to your active social media apps. Keeping them connected to your active app keeps open a possible security hole that someone can take advantage of.
Day 12: Set up your device so you can find it (and wipe out the data) in case of loss
If you have an iOS device, Find My Phone is an app you need to sign into using your Apple ID because it will be your savior in case you lose your device.
For Android users, Google has its Android Device Manager (ADM).
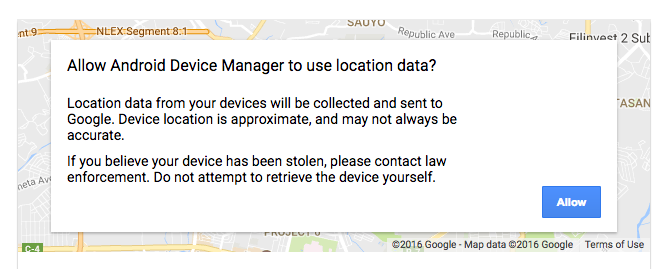
You don’t need to download an app. You can use ADM using a web browser as long as:
- Your device is connected to your Google account.
- Your device has access to the internet.
- You allowed Android Device Manager (ADM) to locate your device (turned on by default).
- You allowed ADM to lock your device and erase its data (turned off by default).
This article gives more details on how to track an Android phone.
Device-tracking features are very useful. Depending on which one you use, it can give a fairly pinpointed location of your device. You can opt to ring it or report its location. You can also opt to wipe out the data remotely, a great feature when you have confidential information on the device.
So there you are — 12 different things I believe you can do so your Christmas holiday makes you Cyber-Mas Secure for 2017. Good luck securing your online devices and accounts. Let’s make 2017 a more cybersecure year.
This post is supported by a writing grant from the Philippine Center for Investigative Journalism (PCIJ)
About The Author

Jane Uymatiao
Jane T. Uymatiao is known as @citizenjaneph. She spent more than 15 years as an IT auditor/consultant at an accounting firm and another 2.5 years as VP-Head of a bank's Corporate Planning Division. She has been blogging for about 16 years now and is one of the early adopters of social media. She believes in active citizen engagement, pushing for transparency and good governance, and is often tapped to speak on social media-related topics. Her personal blogs are: yoga and wellness (yoginifrommanila.com), tech (titatechie.com), lifestyle (philippinebeat.com), and personal (janeuymatiao.com)
Jane has a Master’s degree in Business Administration, major in International Business with a focus on Strategic Management, from the Wharton School, University of Pennsylvania. She is also a certified yin yoga teacher. More details at www.linkedin.com/in/janeuymatiao
Updated: August 2022
The 12 days of Cyber-Mas Secure (Part 2)
Read Part 1 of The 12 Days of Cyber-Mas Secure here.
Day 5: Review your privacy settings
Use the privacy settings of apps such as Facebook and Twitter to review who can see your posts. Facebook, for example, now has a security feature where you can change public posts into posts seen only by a select audience. The images below show how you can select “Limit Past Posts” to change old posts to just Friends.
Be aware that many other apps have default settings that may be less private than you would want so spend time checking them all.
Day 6: Review extent to which you disclose location
Rule of thumb: If there is no need to disclose your location, opt not to.
Some people love to geotag themselves – where they dined, where they traveled, where they are at the moment. If you are one of those who do this, be aware that your pattern of movements can give you away. Someone who is able to gain access to your locations from different apps can piece together a lot of things about yourself.
Location-based apps like Waze and Google Maps require access to your location but you can always tweak your settings so that you only allow access while using the app. Swarm, for example, is an app that lets you check into places with friends. This is the time to review who you accepted as friends in Swarm (and do some purging, if necessary) because those persons will know a lot about your dining, travel, and personal preferences. If you really want to check in, do so only AFTER you have left the place.
Long holidays like the Christmas break are also the times when bad elements are on the lookout for homes to target. Do not post your travel plans or vacation photos online while you are away.
Day 7: Run antivirus and security software
Does your laptop or mobile device have a good antivirus and/or privacy software? It’s time to get yourself one like Avast, AVG, Norton, McAfee or one of the other popular antivirus software in the market.
Set scheduled antivirus scans so it automatically scans regularly.
Day 8: Backup, backup, backup
This cannot be emphasized enough. If the contents of your mobile devices and laptops are crucial to your business or daily life, you cannot afford NOT to have backups.
This season, backup your contacts, important files, and applications. Mac users can do this using Time Machine. Cloud backups are also great but do so only with platforms that are known to have tight security measures. iCloud, Dropbox, Google Drive are some of the well-known platforms for keeping backups. If you have a portable external drive, you can also manually copy important files to it.
Day 9: Use disposable email addresses
This tip is not too popularly followed but it is one that is highly recommended if you want to reduce the amount of spam email you get — Use a disposable email address.
The moment you fill out online forms, subscribe to a newsletter, avail of that free ebook, or sign up for any online service, an email address has to be provided. If you regularly provide your primary email address for these activities, you may find your email overwhelmed by spam. There are many sites that offer disposable or throwaway email addresses. Personally, one of the sites I use is Tutanota. Creating disposable email addresses is very easy with Tutanota and your email mailbox is encrypted too.
Day 10: Activate automated alerts
An effective security measure that allows you to immediately react to a possible hack or intrusion into your accounts is to automate alerts – by SMS, email and/or mobile notification. Notifications can be bothersome at times, especially if you get too many. But there are some that you will be thankful for. Activate alerts for the following types of activities, among others:
Day 11: Revoke access by rarely used apps
You may have linked some apps years ago that you no longer actively use or which may have slowly faded away into oblivion. Check all your app settings and revoke access by these apps to your active social media apps. Keeping them connected to your active app keeps open a possible security hole that someone can take advantage of.
Day 12: Set up your device so you can find it (and wipe out the data) in case of loss
If you have an iOS device, Find My Phone is an app you need to sign into using your Apple ID because it will be your savior in case you lose your device.
For Android users, Google has its Android Device Manager (ADM).
You don’t need to download an app. You can use ADM using a web browser as long as:
This article gives more details on how to track an Android phone.
Device-tracking features are very useful. Depending on which one you use, it can give a fairly pinpointed location of your device. You can opt to ring it or report its location. You can also opt to wipe out the data remotely, a great feature when you have confidential information on the device.
So there you are — 12 different things I believe you can do so your Christmas holiday makes you Cyber-Mas Secure for 2017. Good luck securing your online devices and accounts. Let’s make 2017 a more cybersecure year.
This post is supported by a writing grant from the Philippine Center for Investigative Journalism (PCIJ)
Related Posts
Osama Bin Laden- “I will never forget”
Why the arrest of Maria Ressa is worrisome and why we need to speak up
Something’s Fishy with Kabataan Party List’s Petition
About The Author
Jane Uymatiao
Jane T. Uymatiao is known as @citizenjaneph. She spent more than 15 years as an IT auditor/consultant at an accounting firm and another 2.5 years as VP-Head of a bank's Corporate Planning Division. She has been blogging for about 16 years now and is one of the early adopters of social media. She believes in active citizen engagement, pushing for transparency and good governance, and is often tapped to speak on social media-related topics. Her personal blogs are: yoga and wellness (yoginifrommanila.com), tech (titatechie.com), lifestyle (philippinebeat.com), and personal (janeuymatiao.com) Jane has a Master’s degree in Business Administration, major in International Business with a focus on Strategic Management, from the Wharton School, University of Pennsylvania. She is also a certified yin yoga teacher. More details at www.linkedin.com/in/janeuymatiao Updated: August 2022